How can a mobile phone be hacked?
Is my phone hacked? This is a question you probably haven’t asked yourself, and it could cost you a lot. We store important personal information on our mobile phones – from photos to bank accounts and various passwords. We access social networks, emails, send documents, and information via mobile. If someone got hold of this information without authorization, it could cause us great damage. The easiest way a mobile phone can be hacked is to install certain programs like SpyPhoneApp, Spyzie, or Spyer. It is enough for your unlocked phone to be in the wrong hands for just a few minutes and the hacker will have access to your calls and messages via social networks.
These are programs that, mostly in the West, employers install on the official phones of their employees to monitor their business communication and protect their business.
Another way to hack a mobile is through open Wi-Fi networks in restaurants, cafes, or public places. That is why the use of such an Internet is not recommended.
Another way is via an SMS containing a link. If you click on a link in a malicious message, you are starting to download an application that will infect your phone and give the hacker access to your phone.
What are the signs that a mobile phone has been hacked?
There are several signs that your devices (phone) may be hacked:
You have found applications that you did not install yourself. Phone manufacturers and providers can sometimes install certain applications when updating devices. However, it is always better to check if it may be malicious applications. If they were not installed by you, the manufacturer, or the operator, it must be a hacker.
The battery is running out too fast. If the battery on your phone suddenly discharges very quickly, there must be a reason for that, and it can be a malicious application that runs in the background all the time and steals your data.
These applications are designed to activate themselves, and the user does not even know that they are installed. However, their operation leaves a mark on battery consumption.
You can pick up some malicious malware or virus when visiting an unprotected website that doesn’t have a proper SSL Certificate. The phone runs slower. In addition to increased battery consumption, background hacking applications consume mobile phone processor resources. The result is the slow operation of the device, which is under heavy load.
The phone heats up or restarts on its own. And that even happens when you’re not doing anything on it. This is a sign that there is an application running in the background and drawing on phone resources. This can be connected to a restart of the phone that happens by itself, calls, or SMS messages that are performed independently or applications that turn themselves on and off, and one of the signs is the increased consumption of megabytes of your mobile internet.
Echo during the conversation. If during the call you hear your or the other person’s voice echoing or there are noises and sounds that you have not heard before, you may be a victim of a hacker who is monitoring your phone or eavesdropping on conversations.
You have problems with the email. If the emails you send, either from your phone or your computer, end up in spam, it could be a sign that someone is using your mail without authorization and has set it up to work through some unauthorized servers.
Today, everyone has a cell phone. This device has become the primary means through which we communicate with others, check the balance on the bank account, order products online. That is why mobile phones are often the target of attacks by hackers who want to access users’ data to misuse it.
Passwords and the role of password managers
Passwords on most current websites must be longer than eight characters, must combine letters and numbers, and sometimes require uppercase and lowercase letters. There are more and more places we visit. It’s getting harder to remember so many passwords. Is there an elegant solution? It exists in the form of a password protection and secure use program! Storing usernames and passwords in a plain text file is simply not secure. Admittedly, most antivirus and antimalware software easily handle the methods of classic keyloggers, but something can still breakthrough. Admittedly, things like this rarely happen, but the way described is simply not comfortable. In addition to stealing passwords, forgetting about them can be a big problem.
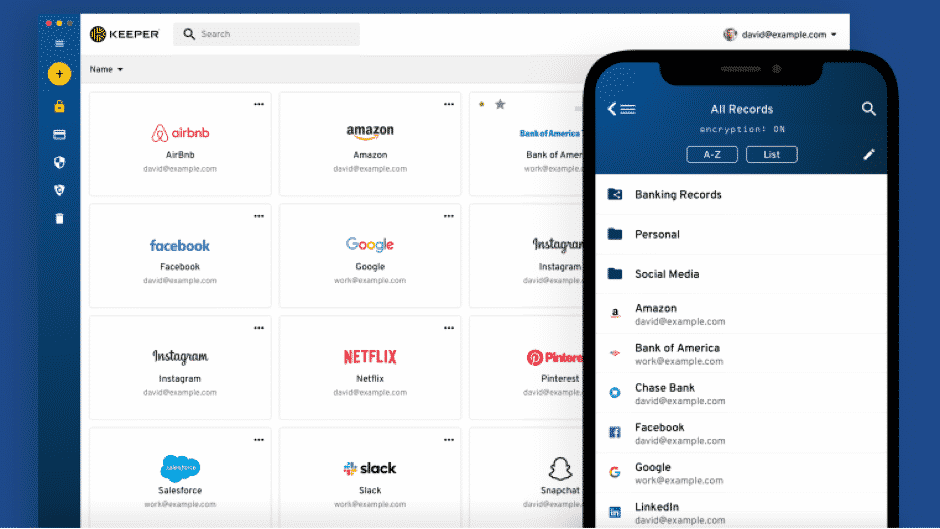
Many sites offer to reset or send a password to an email address, but if that’s not the case, then what? Fortunately, there are much better methods for securely remembering passwords. These are specialized programs that will help you with that, and the offer of such programs is more than satisfactory. Cancel passwords – for many internet users, this would be the right solution. But it’s not that simple. The combination of username and password is the most common form of login on the Internet. Keeper Password Manager & Digital Vault remembers all our passwords and loads them. Good password management programs, like this one, make sense for passwords that are very difficult to crack. A lot of different features and add-ons you can find out here. The advantage of such a manager is that to access all passwords, it is enough to type in the master, the so-called master password. And it must be chosen especially well because if the master password is found out, other data and passwords will be in danger. That is his complete digital life. Other benefits include ease of use of the interface, two-factor authentication, and automatic filling of files and queries.
Tips for using your mobile device safely
Use the screen lock option. As is generally known, if you do not use the device screen lock option with a PIN, pattern, or password, no layer of protection protects the data on the device in case the device is not with you. Additional recommendation – if you use a pattern to unlock, it is recommended to regularly clear the screen of the device to prevent the performance of the so-called. smudge attacks.

Do not connect to insecure networks. Connecting to the networks of restaurants, public places or other open wireless networks can be risky, especially if you are transmitting sensitive data. If you need to use such networks, it is recommended to use a virtual private network (VPN).
Use a device from a manufacturer that updates regularly. The timely response of the manufacturer and the prompt issuance of patches, especially those related to security vulnerabilities, should be taken into account when choosing a device.
Data storage encryption. Device data encryption generally uses a much more complex cryptographic algorithm than the screen lock itself. This protects your data in the event of loss or theft of the device.
Lock the SIM card. Unlocking the SIM card with a PIN does not significantly reduce the user experience because it only needs to be entered when starting the device, and as well as data encryption and screen lock provide an additional layer of protection in case of loss or theft of the device.
Turn off location if you’re not using it. Although this is not directly related to the security of your device, the included location service threatens your privacy. Besides, disabling this option reduces battery consumption and data transfer.
