Cybersecurity is no longer defined by a single tool, platform, or perimeter. In 2026, it has evolved into a layered discipline—one that reflects the complexity of modern business environments, distributed workforces, and increasingly sophisticated cyber threats.
For small and mid-sized businesses, this shift presents a critical challenge: how to build enterprise-grade protection without the resources to do so. This is where managed IT providers are stepping in—not just as support vendors, but as architects of comprehensive cybersecurity ecosystems.
At the center of this evolution is the 7-layer cybersecurity model, a structured approach that reflects how today’s most effective defenses are designed, implemented, and maintained.
Why Single-Layer Security No Longer Works
For years, businesses relied heavily on perimeter defenses—primarily firewalls and antivirus software—to protect their environments. That model has become obsolete.
Modern attacks are multi-vector and often bypass traditional defenses entirely. Phishing campaigns compromise user credentials. Ransomware exploits unpatched systems. Threat actors move laterally across networks once inside, targeting backups, cloud systems, and identity infrastructure.
According to IBM’s Cost of a Data Breach Report, the average cost of a data breach reached $4.45 million globally, highlighting the financial impact of inadequate security strategies.
The result is clear:
No single control can adequately protect a business environment.
Instead, security must be layered—designed to detect, prevent, and respond to threats at multiple levels simultaneously.
The 7 Layers of the Modern Cybersecurity Stack
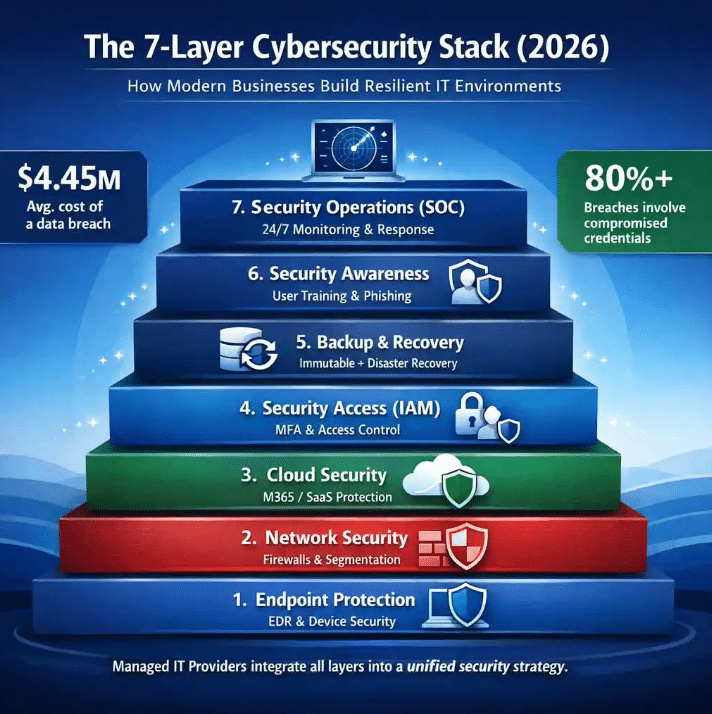
Managed IT providers are increasingly standardizing cybersecurity around a multi-layered architecture. While implementations vary, the most effective models consistently include the following seven layers:
1. Endpoint Protection and Detection
Endpoints remain the most common entry point for cyberattacks. Laptops, desktops, and mobile devices are constantly exposed to phishing, malware, and exploit-based attacks.
Modern endpoint security goes beyond traditional antivirus, incorporating:
- Endpoint Detection and Response (EDR)
- Behavioral monitoring
- Real-time threat isolation
This layer serves as the first line of defense, identifying and containing threats before they spread.
2. Identity and Access Management (IAM)
Compromised credentials are now one of the leading causes of breaches. As businesses adopt cloud platforms and remote work models, identity has effectively become the new perimeter.
According to Verizon’s Data Breach Investigations Report, over 80% of breaches involve stolen or compromised credentials.
This layer includes:
- Multi-factor authentication (MFA)
- Conditional access policies
- Privileged access management (PAM)
Strong identity controls significantly reduce the risk of unauthorized access—even when credentials are exposed.
3. Network Security
While the traditional perimeter has evolved, network security remains a critical component of defense.
Modern network security includes:
- Next-generation firewalls
- Intrusion detection and prevention systems (IDS/IPS)
- Network segmentation
These controls help limit lateral movement and contain threats within isolated segments of the network.
4. Cloud Security
As businesses migrate to platforms like Microsoft 365 and other cloud environments, securing cloud infrastructure has become essential.
This layer focuses on:
- Configuration management and hardening
- Monitoring for suspicious activity
- Data access controls
Misconfigured cloud environments are a leading cause of data exposure, making this layer especially critical.
5. Backup and Disaster Recovery
Ransomware has fundamentally changed how businesses think about backups. Today, backups are not just a recovery tool—they are a core cybersecurity control.
Modern backup strategies emphasize:
- Immutable backups
- Offsite and air-gapped storage
- Rapid recovery capabilities
In many cases, the ability to recover quickly determines whether a business can survive a cyber incident.
6. Security Awareness Training
Technology alone cannot prevent cyber incidents. Human behavior remains one of the most significant risk factors.
This layer includes:
- Ongoing phishing simulations
- Employee training programs
- Security policy reinforcement
Educated users act as an active defense layer, reducing the likelihood of successful social engineering attacks.
7. Security Operations and Monitoring (SOC)
Even with strong preventative controls, threats can still penetrate systems. Continuous monitoring is essential for early detection and response.
This layer typically includes:
- 24/7 security monitoring
- Log aggregation and analysis
- Incident response capabilities
A Security Operations Center (SOC) enables businesses to detect and respond to threats before they escalate into major incidents.
How Managed IT Providers Are Operationalizing This Model
For many organizations, building and maintaining a 7-layer cybersecurity stack internally is not feasible. It requires specialized expertise, continuous monitoring, and integration across multiple technologies.
Managed IT providers are addressing this gap by delivering:
- Fully integrated security stacks
- Standardized frameworks aligned with industry best practices
- Ongoing management, monitoring, and optimization
More importantly, they are aligning cybersecurity with broader business objectives—ensuring that protection strategies support uptime, compliance, and long-term growth.
The Shift from Tools to Strategy
One of the most significant changes in recent years is the shift from tool-based security to strategy-driven security.
Businesses are no longer asking:
“What antivirus should we use?”
They are asking:
“How do we reduce risk across our entire organization?”
This shift reflects a growing understanding that cybersecurity is not a product—it is an ongoing process that requires alignment between technology, people, and operations.
Looking Ahead: Cybersecurity as a Business Function
As cyber threats continue to evolve, cybersecurity is becoming deeply embedded in business operations. It influences everything from vendor selection and compliance to insurance eligibility and customer trust.
The 7-layer model represents more than a technical framework—it reflects a broader shift toward resilience.
Organizations that adopt this approach are not just better protected—they are better prepared.
And in today’s threat landscape, preparation is what ultimately defines success.
About the Author
Matt Kahle is President and Co-Owner of Real IT Solutions, a Michigan-based managed IT and cybersecurity provider. With decades of experience helping businesses navigate technology risk, Matt focuses on delivering proactive, security-first IT strategies that reduce downtime, strengthen resilience, and support long-term growth.
