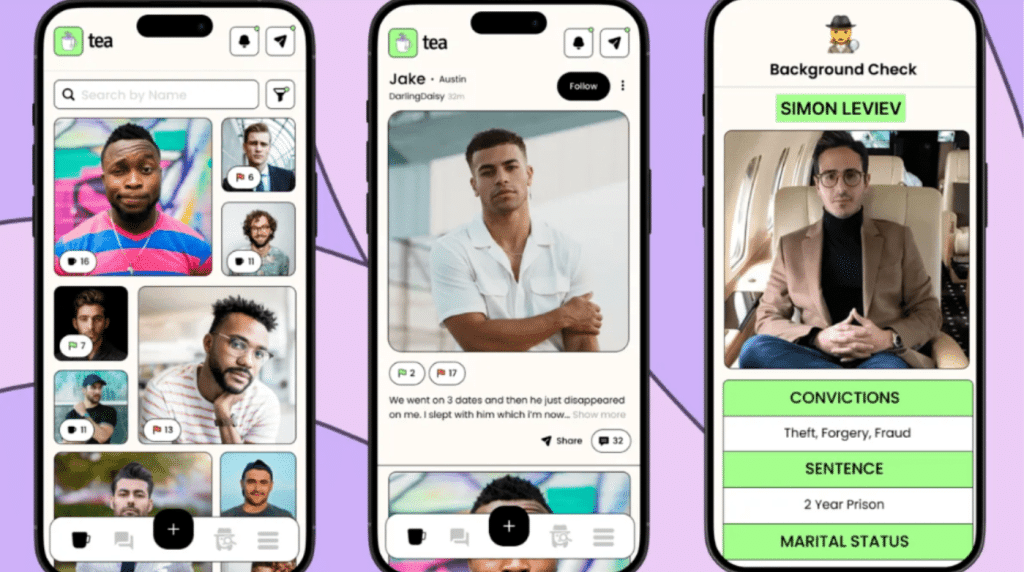
Anonymous “dating review” platforms are often framed as safety tools. But once posts identify a real person—by name, photo, location, workplace, or other personal identifiers—privacy exposure can shift from “online commentary” to potentially actionable harm under U.S. law.
This article explains how the U.S. common law right to privacy may apply to identity-linked posts on Tea-style apps, what claims can arise, and how individuals can protect themselves through verification and documentation.
1) U.S. Common Law Right to Privacy: The Basic Framework
In the U.S., many privacy disputes—especially those involving personal exposure, humiliation, and identity misuse—are pursued under state tort law, not a single federal privacy statute. Common law privacy is often described as the right to be free from unwarranted publicity, exploitation of one’s identity, publicizing private affairs with no legitimate public concern, or wrongful intrusion that causes mental suffering, shame, or humiliation.
This area is typically discussed as:
- Tort privacy (civil claims for damages), and
- Constitutional privacy (limits on government intrusion)
Tea-style app disputes most often implicate tort privacy.
2) The Four Privacy Torts—and Where Tea-Style Posts Create Risk
Privacy law commonly recognizes four invasion types. Tea-style posting can implicate each when content is identity-linked:
A) Intrusion Upon Seclusion
Unreasonable intrusion into someone’s private life (for example, invasive data gathering, doxxing-style conduct, stalking, or accessing private accounts).
Key question: would the intrusion be highly offensive to a reasonable person?
B) Appropriation of Name or Likeness (Misappropriation / Right of Publicity)
Using someone’s name, photo, or identity without consent—especially for commercial benefit. If identifiable images or names are used to drive engagement, subscriptions, or advertising value, risk increases depending on the state.
C) Public Disclosure of Private Facts
One of the most relevant theories for “dating review” posts. Liability risk rises when a post publicizes private facts that are not of legitimate public concern and would be highly offensive if disclosed.
Common red flags include: home address, workplace identifiers, family details, medical information, explicit sexual details, or other sensitive personal data.
D) False Light
Publicity that places someone in a misleading position that would be highly offensive (for example, implying criminality, abuse, or dangerous conduct through selective framing). Some jurisdictions recognize false light; others do not—so state law matters.
3) Damages: What Plaintiffs Often Seek
In privacy tort cases, damages commonly track the interest invaded:
- Intrusion: loss of seclusion and emotional distress
- Appropriation: value of identity misused
- Private facts / False light: reputational harm, humiliation, emotional distress
Courts have long recognized that privacy invasions can cause real-world injury, not merely “online discomfort.”
4) The Practical Problem: Verification and Evidence Preservation
For individuals who suspect they were posted, the destabilizing issue is often procedural: you may not know where the content is, whether it exists, or what reporting requires.
A documentation-first approach typically starts with:
- Verify whether identity-linked content exists
- Preserve evidence (screenshots, timestamps, direct references)
- Use official reporting/takedown channels and retain submission records
Some individuals begin with a lookup resource (for example, Tea Checker) to identify potential matches and obtain a direct reference before proceeding through official processes.
Evidence checklist (basic):
- Capture screenshots including username, date, and context
- Save URLs/direct references and record timestamps
- Separate what is stated from what is implied
- Avoid escalation that amplifies visibility
- Use official reporting channels and keep records
If content includes threats, doxxing, impersonation, or explicit sexual material, consult counsel about rapid escalation options.
5) Beyond Common Law: State Privacy Statutes
In addition to tort law, many states regulate personal data handling (collection, sharing, deletion rights, and sensitive data). Whether a Tea-style app is covered depends on user location, data practices, thresholds, and statutory definitions. Because these laws vary and evolve, compliance risk can increase when platforms enable identity-linked targeting or fail to provide meaningful rights mechanisms where required.
Conclusion
Anonymous dating disclosures may serve legitimate safety goals, but legal exposure increases when anonymity is paired with identifiable targets and reputation-altering narratives. The four privacy torts—intrusion, appropriation, public disclosure of private facts, and false light—remain a core framework for evaluating harm, with state privacy statutes adding potential compliance obligations.
When identity-linked private exposure spreads, it may not be “just online.” It can become legally consequential.